Hour six in a borrowed parking lot, fifty feet from the building, two of us in a sedan with directional antennas pointed at the cafeteria. Not one employee had so much as glanced our way. That was the moment we realized this engagement was already over. We just had to walk inside and prove it.
The client was a Fortune-rated US enterprise, big enough to have its own zip code and its own internal bus route. The scope was a black-box red team with a physical component, two-person team, week-long timebox, light scoping. They wanted to know what a motivated outsider could do in seven days. We were happy to tell them.
What follows is sanitized. The client is not named, the partner on the engagement is not named, the location and dates are deliberately vague. The tradecraft, the scripts, and the moments are real and unembellished.
Day one: the sit-and-watch
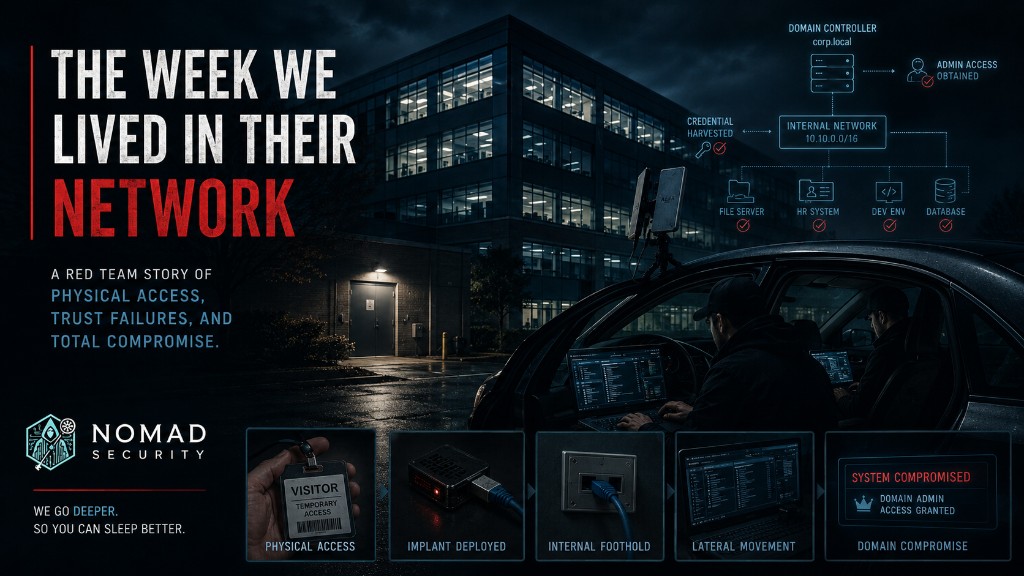
The night before, in a hotel room three miles from the target, we built our kit. A Raspberry Pi flashed and configured to call out via three independent channels (reverse SSH on 443, OpenVPN, and SSH tunneled inside HTTP via Corkscrew, in case both of the first two were filtered). A Proxmark loaded with common HID and MIFARE Classic profiles. A clutch of Malduino USB drops with Windows and macOS payloads. And a homemade badge: a printed photo behind a clear ID-holder window, sized to look right from across a hallway.
The two most useful tools were free. Google Street View, pulled up on a hotel-room laptop, had captured the entire campus in enough resolution that we could count the cameras over the front door, identify the cafeteria patio as a likely smoke spot, and pick out the side entry that did not appear on the company’s printed visitor map. LinkedIn was the second. A thirty-minute scroll surfaced two employees posing for happy-hour pictures with their badges hanging from lanyards in fully readable glory. Now we had the badge template.
Morning of day one, we parked in the lot of the building next door, roughly fifty feet from the side cafeteria entrance. Antennas in the windshields, laptops on the dashboards, coffee cups multiplying on the center console. Six hours.
The goals were modest. Identify the actual entry points (separate from the listed entry points). Watch foot traffic to map cigarette breaks, which always reveal a convenience door propped or held. Identify CCTV blind spots from the geometry of the cameras. Confirm the badge format the readers expected. Capture any EAP authentication that drifted out to the parking lot.
None of the antennas were subtle. Two grown men in a parked sedan, equipment pointed at an executive office, six hours. The building’s contracted security never approached. No employee asked. The company in the lot we were squatting in did not call. The first finding of the engagement was a culture finding, and we had not entered the building yet.
Day two: the entry that was supposed to fail
The plan was to tailgate through the main entrance, which was guarded, badge-logged, and on camera. We picked the harder of two paths deliberately, because we wanted the client to have a chance to catch us. The cafeteria side door was easier. We would save it.
My partner went in first with our practiced backstop. He waved his (non-functioning) badge at the reader. It beeped, in the way that tells everyone within earshot that the scan failed. The guard looked up and called him over. He scanned again. Same beep. Then he switched to the prepared script.
“Oh god, I think I put it through the laundry last night. I have a meeting in five minutes, my boss is going to kill me. Please.”
The guard let him through after extracting a promise that he would go to facilities for a new badge after the meeting. He went straight for the nearest stairwell to break line of sight, only to discover the stairwell door was badge-required to leave. He stood inside it on a fake phone call until an employee came through, mumbled “see you in the meeting,” and walked out behind them.
An hour later, I came in through the cafeteria side entrance behind an employee on a smoke break. She held the door for me without making eye contact. We were both inside the building in under ninety minutes. Total physical-security tooling deployed: a clipboard, an ID-badge holder with a piece of paper in it, and a confident face.
Day three: the foothold
We found an unoccupied office in a corridor of unoccupied offices, a pattern we now expect in any post-pandemic enterprise floor plan. We set up.
The Pi went behind a desk, plugged into the wall jack in place of the desk-phone power cord. We had three independent C2 channels prepared because we expected to lose two of them to outbound filtering. Reverse SSH on port 443. OpenVPN. SSH tunneled inside HTTP via Corkscrew. All three came back inside thirty seconds. We had not even made the office door look untouched yet.
Out of curiosity more than plan, we started Responder for ten seconds. A service account broadcast its hash to us within that window. The crack ran on a laptop and finished in under ten seconds. We had domain admin.
From the moment my partner walked through the front door to a working domain admin shell: under three hours. We could have left the building right then and the engagement would have been a complete success on paper.
We did not leave.
Day four: the after-hours tour
We waited in the unlocked office until the building emptied around 7pm, then started walking. What we found mattered more than the domain admin shell, because the domain admin shell was a technical finding, and technical findings get triaged. What we found on the night walk was a culture finding, and culture findings are what actually move security programs.
Sticky notes with passwords on monitors, more than thirty in one walkthrough. Filing cabinets unlocked, containing tax records, signed NDAs, and HR memos with names and Social Security numbers in plain text. A door with a biometric reader leading into a server room, which we did not bother to enter, because the equally-restricted door labeled BADGE PRINTER ROOM next to it was unlocked, and the desk inside that room held the credentials and software needed to print employee IDs.
We printed our own. Two laminated badges with names and photos that did not appear on any real org chart, made on the spot with the company’s own seal.
Three hours of after-hours wandering through a Fortune-rated enterprise’s headquarters produced exactly one human encounter. A janitor walked into a room where I was actively picking a lock with picks scattered across the floor in front of me. He made eye contact. He said, “I need to empty this trash can and then I’m leaving.” He did neither. He left.
There is a name for that response in security training material. The name is “normal.”
Day five and six: the cocky walkaround
With our self-printed employee badges hanging from our necks, we spent the next two days walking the building during business hours, in plain sight of every camera and every guard, asking nobody for help and being asked for help by nobody.
We started getting cocky. We were waving at cameras. We sat in a conference room and listened to executive meetings on a microphone we had wired into a Pi planted in a hallway flowerpot (the recording capability was scoped into the engagement; that part is not as wild as it sounds). We were trying to get caught. We did not get caught.
By the end of day six, the question was not what else we could compromise. It was when we should stop.
Day seven: the handoff
On the morning of day seven, my partner walked into the CISO’s office, left two business cards and two laminated employee ID badges on the desk, walked out, and we drove home.
What this engagement actually said about the client
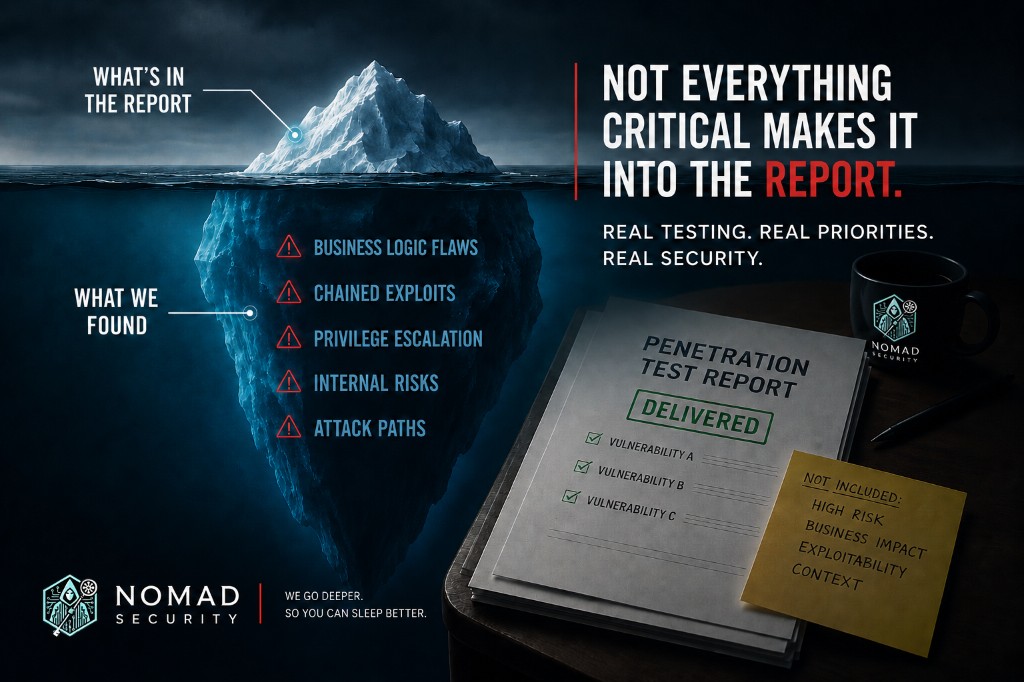
The technical surface was trivially exploited. Three hours from front door to domain admin, a single Responder run, a service account with too much privilege and a password that lost a fight with a laptop. Those are findings. They get fixed. A vendor sells a product, a control gets implemented, an auditor signs a box.
The real surface was organizational, and the real surface was much, much larger. People in the building did not challenge strangers. Filing cabinets were not locked. Workstations were not locked. Passwords were not put away. The badge-printer room (a more critical asset than the server room next door, because controlling badge issuance is controlling identity) was treated as office furniture. Visitors with broken badges were waved through on the strength of an embarrassed-sounding story.
Every one of these is a culture problem dressed in process clothing. The fix is not more cameras and more readers. The client we tested had cameras and readers. They had a biometric door on the data center. They had a security operations center. They had bought the things you are supposed to buy.
The fix is closer to the fix in any culture problem: leadership that publicly cares, training that is uncomfortable rather than reassuring, and consequences that are real. The people who let us in (the guard who accepted the laundry story, the employee who held the cafeteria door, the janitor who walked away from the lock picks) all behaved exactly as their corporate training had prepared them to behave. Their training had prepared them to be polite, to not make scenes, and to defer to anyone confident-looking.
That is the actual finding. The people did their jobs. The jobs, as they had been described to them, were the wrong jobs.
If you run security at a company with a physical campus, your office would do most of the same things. Probably not all. The badge-printer room is uncommonly bad and most enterprises have caught that one. But the laundry story works almost everywhere. The cafeteria door works almost everywhere. The unlocked filing cabinet works almost everywhere. The janitor walks away almost everywhere.
What we’d do this week
Five questions to ask your team this week. Ask them in this order; each one builds on the last.
- If a stranger walked into the office today wearing a lanyard, how long before someone challenged them? Not “would they.” How long. If the honest answer is “depends who is at the front desk that day,” you have your first finding.
- Who has the authority to override your visitor process, and what is their training? The guard who let my partner in had the authority to deny entry and the training to be polite. Those two things are in tension; the polite training won. Whose training, in your building, is in tension with whose authority?
- Where is your badge-printer room, who can enter it, and is the printer credential stored on the same desk as the printer? If you don’t know, find out before Friday. The badge printer is a higher-criticality asset than your domain controllers, because it manufactures identity.
- When was the last time someone on your team ran a tailgating exercise that involved actually walking in, not a tabletop? Tabletops produce reassurance. Walk-ins produce findings. Pick a Tuesday.
- What is your training actually teaching the people in your building? Read the script your awareness vendor wrote. Read it as if you were a new hire. Notice how many times it tells the reader to be helpful, polite, or non-confrontational. Notice how many times it tells the reader to challenge a stranger. Compare the counts.
The answers are uncomfortable. That is the point. Uncomfortable training is the only kind that changes behavior in the moment when the laundry story arrives at your front door.